Smishing: How to Combat the New Phishing Trend
December 23, 2021
By Rhia Prajes
Although Phishing is one of the oldest tricks cybercriminals use and protections against it are improving every day, perpetrators are getting craftier by pursuing a new channel: SMS.
Why SMS?
Since it is a less conventional method, SMS Phishing, or Smishing, is being used by threat actors to lure victims and catch them off-guard. Compared to email, there has been less investment in security tools to validate text messages against phishing and block links to malicious websites. At the same time, SMS Marketing become more common over the last few years and provides a backdrop of “noise” for these phishing attacks to blend into. Due to these factors, SMS has been seen by threat actors as a more effective method to reach targets and proliferate malware.
Recent Attacks
This year, a Smishing scam called TangleBot became rampant detailing COVID-19 information via text, only to download smartphone based malware which exported confidential information. In the blink of an eye, it can harvest data from contacts, audio and video recordings, call logs, and even internet access. This poses a great risk of identity theft, data hijacking, and blocking calls to motivate payment of ransoms or facilitate espionage.
Examples of SMS Phishing Taking Advantage of the COVID-19 Crisis:[row] [column span=”4″]
[/column] [column span=”6″] [/column] [/row]What Do they Look like?
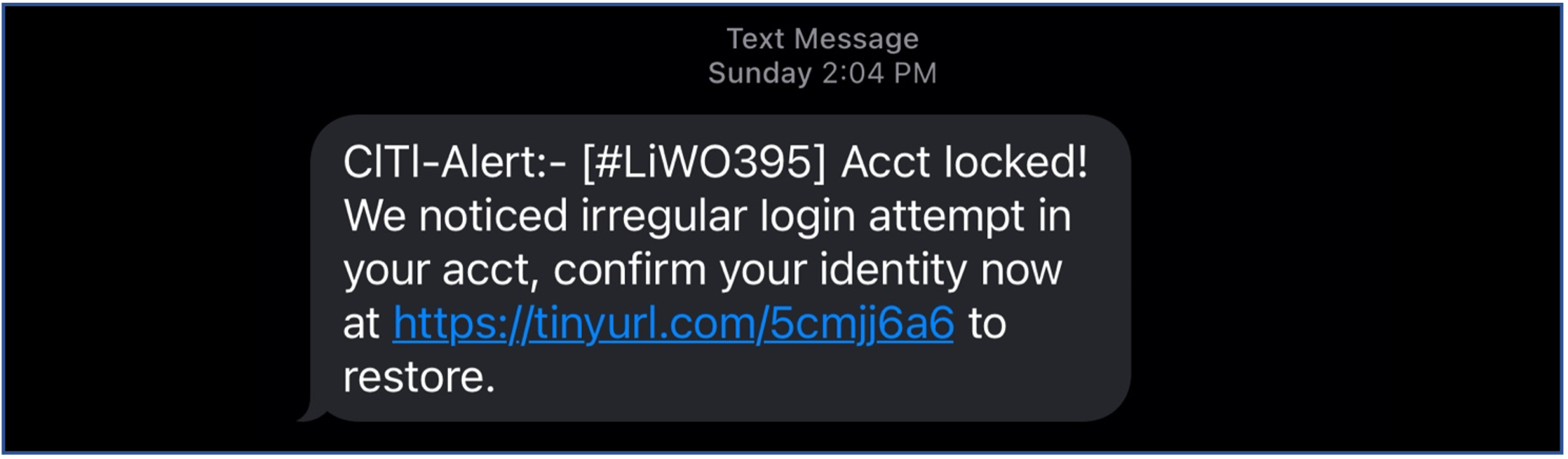
Overall, the common elements of Smishing are similar to that of traditional Phishing: short, alarmist text messages with an unverified link attached, and—oftentimes—poor spelling and grammar. Just as perpetrators use COVID-19 as a trap for Smishing, there are many other formats that threat actors may use to trick their victims. For example, they may be presented as package delivery messages, online purchase confirmation, warnings for bank accounts, or illicit messages. Some targeted Smishing campaigns may even contain personal information to lure targets into replying or calling the sender.[row] [column span=”4″]
[/column] [column span=”4″] [/column] [column span=”4″] [/column] [/row]How to Protect Yourself from SMS Phishing
The best and simplest way to protect yourself from a Smishing scam is to avoid following links from unverified senders. Even if the message is legitimate, the needed information is likely to be available elsewhere and can be verified by logging into an account. In the case of a clear SMS phishing attempt, it is best to ignore the message and block the sender.
With personal becoming devices so common in the workplace, however, it is important to know the best defenses available to combat Smishing at work. Here are some of the common best practices individuals and businesses can use:
Cybersecurity Training:
As mentioned, having the right knowledge can make all the difference between identifying a malicious text and becoming a victim. By holding regular training to educate your staff on changing trends, such as the emergence of SMS Phishing, they can be best informed on how to recognize these threats and hit the Block button.
SMS Phishing Tests:
Many cybersecurity firms and platforms today can conduct fake phishing campaigns to help organizations assess their preparedness. Using these tools, an organization can determine if training should be scheduled, or if any high-risk personnel should have permissions revoked.
Mobile Device Management:
Mobile Device Management can give you additional control over the devices in your organization by requiring employees meet certain criteria to access data, such as encryption, PIN lock In many cases, these criteria may be overridden if an SMS Phishing attack succeeds and block access.
Endpoint Protection:
Endpoint Protection works to help enterprises prevent, detect, and respond to advanced threats. In the event of a successful smishing attack, these tools may have the capacity to remediate a ransomware infection or compromised account, and at the very least provide IT teams with an alert to cut off access.
In Conclusion
With Smishing on the rise, it is imperative for any individual and organization to make use of as many protection and prevention measures as possible. Security awareness must be applied with due diligence whether one is using a personal or a company-owned device. As an expert in Microsoft Cybersecurity, Metro CSG can help you develop a security practice to defend against these new and evolving threats.